Digital Record Audit – цуисфьеуые, 8174850300, Felipewillis Motorcyclegear, Xidhanem Malidahattiaz, How Is Kj 75-K.5l6dcg0
Digital Record Audit presents a structured lens on provenance, attribution, and traceability for ecommerce branding data. The discussion centers on decoding identifiers such as 8174850300 and Kj 75-K.5l6dcg0, then evaluating their completeness, accuracy, and lineage. A methodical workflow is proposed to surface gaps, validate governance controls, and support disciplined remediation. The aim is persistent skepticism tempered by practical steps that preserve autonomy while exposing actionable risk signals, leaving the next step ambiguous and worth pursuing.
What Digital Record Audit Is and Why It Matters
A digital record audit is a systematic process for evaluating the completeness, accuracy, and reliability of electronic records and the systems that manage them. It scrutinizes Digital records, data provenance, and audit cadence to establish credibility.
The effort protects Branding integrity, countering drift, and ensuring traceable lineage; it clarifies controls, reveals gaps, and supports informed freedom through disciplined transparency and verifiable accountability.
Decoding Key Identifiers: 8174850300, Kj 75-K.5l6dcg0, and Beyond
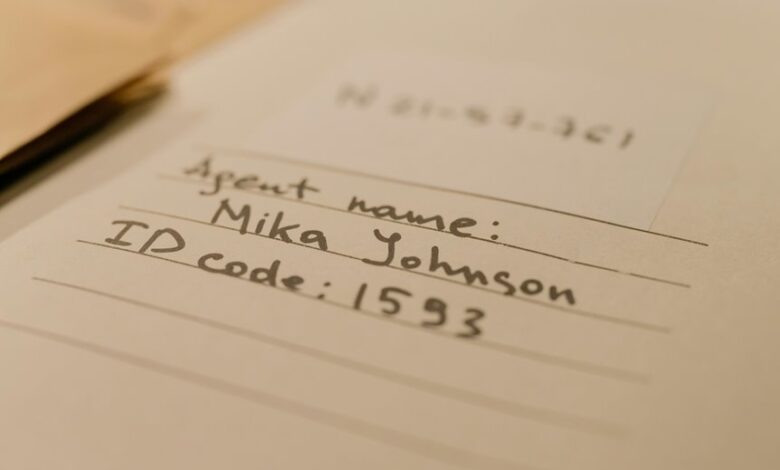
What do the identifiers 8174850300, Kj 75-K.5l6dcg0, and related codes reveal about a digital record’s provenance and integrity? A careful parsing shows decoding keys, data identifiers, and metadata trails underpin traceability. Security practices and governance standards govern interpretation, storage, and verification, mitigating ambiguity. Skeptical assessment emphasizes provenance gaps, cross-checks, and independent auditing to sustain freedom through accountable records.
A Practical Audit Workflow for E-commerce and Branding Data
In practical terms, an audit workflow for e-commerce and branding data proceeds through clearly defined stages: data collection, asset attribution, and verifiable lineage, each with explicit criteria for accuracy, completeness, and timeliness.
The process emphasizes data integrity and stakeholder alignment, demanding skeptical validation, meticulous documentation, and disciplined cross-checks to ensure dependable records while preserving organizational autonomy and freedom.
Security, Compliance, and Actionable Next Steps in Digital Record Audits
Security considerations are foundational to digital record audits, ensuring that data handling, access controls, and governance mechanisms meet established standards before any verification steps proceed.
The analysis remains meticulous and skeptical, identifying security gaps and compliance gaps without assumptive conclusions.
Actionable steps emphasize risk-based remediation, documented policies, and independent validation, preserving organizational freedom while enforcing disciplined, verifiable safeguards and transparent accountability.
Frequently Asked Questions
How Is Data Ownership Determined in a Digital Record Audit?
Data ownership in a digital record audit is determined by explicit contractual terms and applicable law, focusing on data sovereignty and access rights, while remaining skeptical of vendor lock in and ensuring transparent governance, accountability, and nonproprietary control mechanisms.
What Are Common Data Provenance Gaps to Look For?
“Moderation preserves power.” Data provenance gaps include incomplete data lineage, missing or inconsistent metadata, undocumented transformations, and lineage breaks; investigators scrutinize metadata gaps and data lineage to ensure traceability, authenticity, and independent verification for freedom-loving stakeholders.
Which Tools Best Automate Record Integrity Checks?
Automated tools for record integrity checks prioritize cryptographic hashing, tamper-evidence, and automated reconciliation across repositories. For data migration and archival policies, they should support verifiable provenance, schedule-driven scans, and auditable alerts, while remaining skepticism-driven and user-empowering.
How Do Audits Handle Multilingual Product Metadata?
Audits handle multilingual metadata by applying standardized schemas and cross-border compliance checks, ensuring consistent field mappings and translation integrity. They skeptically verify provenance, detect localization gaps, and document methodologies for repeatable, auditable cross-jurisdictional data practices.
What Escalation Paths Exist for Audit Findings?
Escalation paths exist via defined timelines and responsibility matrices, ensuring timely accountability; coincidence underlines how issues mirror organizational roles. Escalation timelines guide urgency, while responsibility matrices clarify ownership, handoffs, and corrective action, fostering disciplined, freedom-respecting audit governance.
Conclusion
The digital record audit yields a disciplined view of provenance, data attribution, and traceable lineage across e-commerce branding. While decoding keys and metadata trails clarifies gaps, skepticism remains essential: correlations must be validated, controls tested, and governance documented. A methodical, risk-based remediation plan should follow, with independent validation to avoid overconfidence. In short, the framework helps prevent surprises, but success hinges on rigorous scrutiny and accountability at every step. It’s a tight ship, but doable.







